Latest News
Jaroslav Seifert (1901 – 1986)
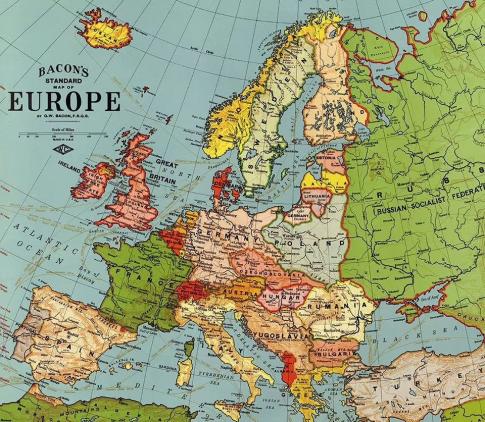
Poet and journalist who was the first Czech to win the Nobel Prize for Literature in 1984.BE; skandale në Parlamentin Europian
Skandali duket se do të zgjerohet përtej Parlamentit Europian...Financing Global Survival
These global challenges are also deepening economic inequality ...The Failure of European Energy Policy
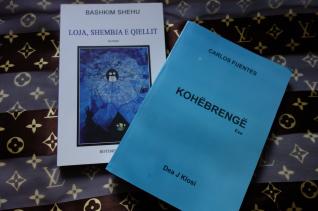
Skyrocketing energy prices are a disaster for the European economy..." Lugjet e Qyqes"
Lukovë ; atmosferë dehëse, pyje të larta, fusha të purpurta, të kuqe...Argjentina / Bota arbëreshe /Messi
Popullsia arbëreshe krijuan stilin e tyre të “gjitonisë”...What Is a Moral Foreign Policy?
... the nature of foreign policy – with its many contingencies and...WEATHER
MONEY EXCHANGE
Top Rated
Featured author
“Gucci”, marka e modës e themeluar në vitin 1921 nga Guccio Gucci në Toskanën italiane ka vendosur të ndërmarrë një hap të rëndësishëm që mund ...
"Everything is very open with a clear clarification of the issues. It was truly informative. Your site is very useful. Many thanks for sharing!"
https://tinyurl.com/yaa5qon4
"I needed to thank you for this wonderful read!! I absolutely loved every little bit of it. I have got you book-marked to check out ...
Great writings here are always and I really I like everything here.
I this like as well:
<a href=https://www.recode.net/users/frank4865>נערות ליווי ברמת גן</a>
It is worth considering present associates, you could also be perfect for each other and you just by no means realised it. While this will ...